Microsoft has been saying that we need to disable SMBv1
which is an old protocol that goes back to Windows XP for networking and sharing.The last windows 10 major update was in April – June 2018,|
Microsoft has disabled SMBv1 on only new installs of Windows 10. (build version1803-17134.137 latest)
Disabling SMBv1 stops networking, sharing.
MOST Important for Everyone
especially those that are sharing data between computers.
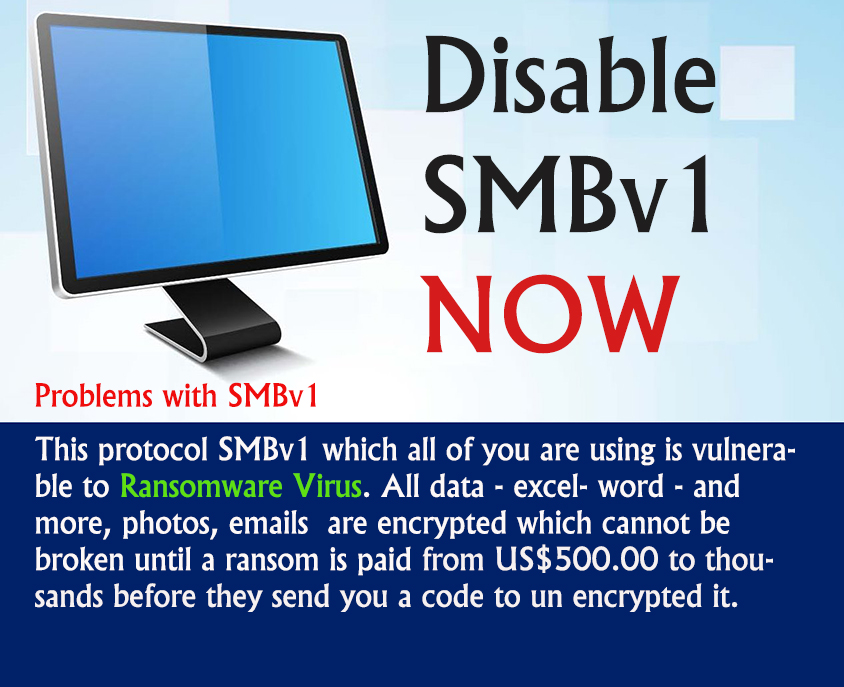
Problems with SMBv1
This protocol SMBv1 which all of you are using is vulnerable to Ransomware Virus.
All data – excel- word – and more, photos, emails are encrypted which cannot be broken until
a ransom is paid from US$500.00 to thousands before they send you a code to un encrypted it.
Personal Experiences with 4 clients
These clients lost all their data, life long Photos and important business and personal files.
Solution
1. Disable SMBv1
2. Use another method of sharing files and folders between computers and devices.
(Took me 2 days to find another method, Microsoft with its technical jargon was difficult to follow)
—————————————————————————————————————————
For those who what to know more
What is Ransomware Virus ??
Ransomware is a subset of malware in which the data on a victim’s computer is locked, typically by encryption, and payment is demanded before the
ransomed data is decrypted and access returned to the victim. The motive for ransomware attacks is nearly always monetary, and unlike other types of attacks,
the victim is usually notified that an exploit has occurred and is given instructions for how to recover from the attack.
Payment is often demanded in a virtual currency, such as bitcoin, so that the cybercriminal’s identity isn’t known.
What is SMBv1 ??
Server message block (SMB) is an application layer network protocol used typically to provide shared access to files and printers.
It is also known as Common Internet File System (CIFS). Most data is transferred via TCP port 445 although, it also uses TCP port 137 and 139.
SMB was first used in Windows operating systems around 1992. Windows Server 2003, and older NAS devices use SMBv1 natively.
It is a very inefficient protocol; Microsoft have advised all customers to stop using SMBv1. SMBv2 was introduced with Windows Vista in 2006
and the latest version is SMB 3.1.1 which was introduced with Windows 10 and Windows Server 2016.
More on RansomWare Virus
Ransomware malware can be spread through malicious email attachments, infected software apps, infected external storage devices and compromised websites.
A growing number of attacks have used remote desktop protocol and other approaches that don’t rely on any form of user interaction.
In a lockscreen variant of a ransomware attack, the malware may change the victim’s login credentials for a computing device; in a data kidnapping attack,
the malware may encrypt files on the infected device, as well as other connected network devices.
While early instances of these attacks sometimes merely “locked” access to the web browser or to the Windows desktop —
and did so in ways that often could be fairly easily reverse-engineered and reopened — hackers have since created versions of ransomware that use strong,
public-key encryption to deny access to files on the computer.
Famous ransomware: CryptoLocker and WannaCry
Perhaps the first example of a widely spread attack that used public-key encryption was Cryptolocker, a Trojan horse that was active on the Internet from September 2013
through May of the following year. The malware demanded payment in either bitcoin or a prepaid voucher, and experts generally believed that the RSA cryptography used –
– when properly implemented — was essentially impenetrable. In May 2014, however, a security firm gained access to a command-and-control server used by the attack
and recovered the encryption keys used in the attacks. An online tool that allowed free key recovery was used to effectively defang the attack.
In May 2017, an attack called WannaCry was able to infect and encrypt more than a quarter million systems globally. The malware uses asymmetric encryption so that the
victim cannot reasonably be expected to recover the (private and undistributed) key needed to decrypt the ransomed files.